What You Need To Know About Petya – The Dangerous Ransomware Spreading Worldwide
A few days ago, a new and nasty piece of ransomware dubbed Petya began spreading across the globe. Based on an exploit that was also used during the WannaCry ransomware attack, Petya locked down machines and demanded payment in the form of $300 worth of Bitcoin. As the cyber attack began to spread worldwide, reports surfaced indicating that it had already impacted IT systems at companies such as Merck, Oreo and other large corporations.
The video below by CNET explains what’s going on:
It has impacted a number of industries, with governments, shipping firms, a petroleum giant and even the Chernobyl nuclear reactor all reporting instances of Petya. “It’s massive,” Christiaan Beek, a lead scientist and principal engineer at McAfee said about the situation in Ukraine. “Complete energy companies, the power grid, bus stations, gas stations, the airport, and banks are being targeted.”
The security researcher continued that he believes Petya has been designed for “speed, and is spreading around like crazy”. Kaspersky Lab’s global research director Costin Raiu tweeted to say the majority of infections seen by his firm had taken place in Ukraine, the Russian Federation, and Poland.
Meanwhile, other experts have confirmed the ransomware has been seen in multiple locations and (like with WannaCry) when a computer is locked, a $300 bitcoin fee must be paid to decrypt the locked systems. The bitcoin wallet listed in the demands has received multiple payments, with a relatively paltry sum of £5,800 being collected at the time of writing. However, email client Posteo, which hosts the account where bitcoin payments are being sent, has closed the address listed in the ransom note. This effectively means those who want to pay the ransom, can’t. In a statement, the German firm says it “does not tolerate any misuse of our platform”.
What Is The Petya Ransomware?
Malware under the name of Petya has existed since 2016, with Symantec saying the version used in this cyberattack has been modified and can spread via a worm.
Researchers have said that although some of the code is shared from the previous versions of Petya, this version is different. It has also been dubbed NotPetya, as a result. Kaspersky says the malware is different to Petya and has been altered for the current attack. Researchers from the firm added it has been designed to have “plausibly deniable cover of ransomware”.
In particular, Petya/NotPetya has been heavily modified to not look like the 2016 version of the ransomware. The Russian security company says Petya is a “complex” cyberattack and said EternalBlue has been modified by whomever created it.
So far, reports of the Petya ransomware are still emerging and a full picture is not known. This increases the potential of early analysis being wrong, and more detailed inspection of the code will reveal greater details of the developing picture. As a result, this story will be updated as more information is confirmed.
Despite the many uncertainties about the ransomware, reports have continued about its spread. UK marketing firm WPP tweeted to say it had been hit “by a suspected cyberattack”. The UK’s National Crime Agency said it is monitoring the situation and working with other companies around the world. The National Cyber Security Centre similarly said it is “monitoring the situation closely”, while the NHS, which was hit hard by WannaCry, said it wasn’t suffering from any “significant” incidents following the spread.
Which Companies Have Been Hit By Petya?
In one of the most high-profile occurrences of Petya ransomware, Ukrainian vice prime minister Rozenko Pavlo tweeted an image of a computer that had been infected and said the “whole network ‘fell down'”. Press agency AFP then reported that Chernobyl’s radiation monitoring system has been switched to manual following an attack.
Shipping firm Maersk said it suffered a cyberattack and that its IT systems are offline “across multiple sites and business units” due to the incident. Russian petroleum company Rosneft also tweeted it had been hit by a cyberattack and has contacted law enforcement authorities.
As the day has progressed, the malware has spread to the US. Pharmaceutical company Merck said it had been hit as part of the global cyberattack.
How Does Petya Ransomware Spread?
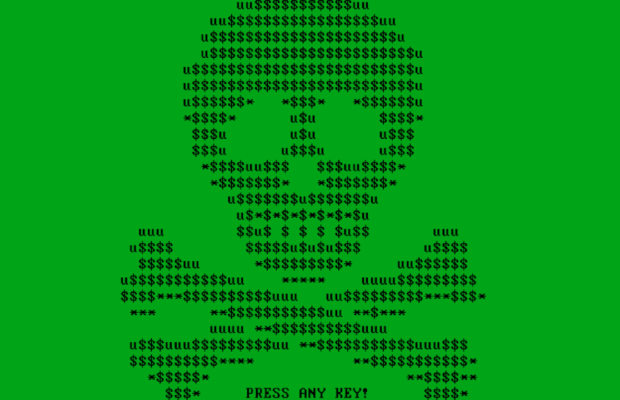
The ransomware, like the majority of strains of the malware, is said to be locking computers that are infected and encrypting files on them. “‘If you see this text, then your files are no longer accessible, because they have been encrypted,” screenshots of the ransomware say. They also demand bitcoin to be decrypted.
Security companies are confident the Petya ransomware uses the same software exploit in Microsoft products that WannaCry was able to exploit. Symantec says it has confirmed the ransomware is using the EternalBlue vulnerability that is believed to have been developed by the NSA. As well as this the Petya strain uses the EternalRomance exploit and has been traced back to Ukrainian software called MeDoc.
Symantec analysts have confirmed #Petya #ransomware, like #WannaCry, is using #EternalBlue exploit to spread
— Security Response (@threatintel) June 27, 2017
Both Symantec and F-Secure say that although Petya does encrypt systems, it is slightly different to other types of ransomware. “Petya is a new ransomware with an evil twist: instead of encrypting files on disk, it will lock the entire disk, rendering it pretty much useless,” F-Secure explains. “Specifically, it will encrypt the filesystem’s master file table (MFT), which means the operating system is not able to locate files.”
Beek adds that Petya has not been disguised with a lot of sophistication. “It is using a fake certificate that is derived from Microsoft’s Sysinternal tools,” he says. “It’s not heavily obfuscated I would say, so it is easy to read through the functionality of the ransomware.”
How To Avoid The Petya Ransomware?
The advice for protecting yourself against Petya applies to many types of malware – make sure you system and apps are updated. The EternalBlue tools exploit flaws in out-of-date software so maintaining your systems will limit these attacks.
It’s also worth investing in at least two anti-virus programs – one free, and one paid for. This is optional but will give you added protection. Set these programs to run regular scans of your system and emails.
Don’t open emails or attachments without confirming they are safe and you know the sender. This should be common practice.
Via WIRED












 © 2024
© 2024
0 comments