Spyse: Cyberspace Search Engine For Fast Data Gathering

Cybersecurity experts have been breaking their backs over how to speed up processes like data gathering. Notoriously the most tedious part of penetration testing is reconnaissance, mostly because of the time that takes to gather data about the target. Here is the solution to this problem – The Spyse cyberspace search engine. They have recently combined all their services into one, promising to entirely oversee the data gathering process so that users don’t need fifty scanners running the same time. The biggest feature of the Spyse engine is its massive database which contains over 7 billion documents, ready for access.
In this article, we will look at how Spyse combined the unique database approach, scan algorithms, and data providing methods saving up time for reconnaissance.
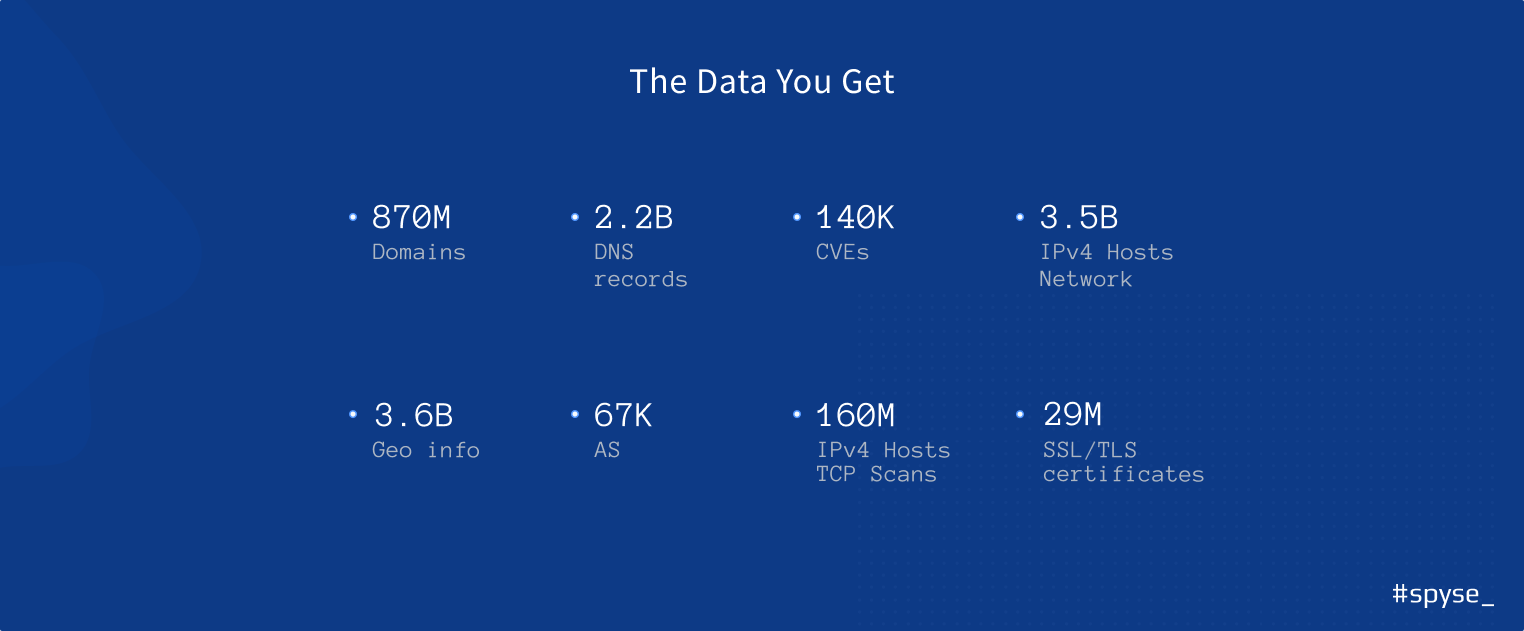
Collecting All Types Of Data
Search engine crawlers scan for data using a sophisticated system of more than ten scanners, each focusing on gathering specific information from various sources in order to supply the most precise results.
Additionally, a 50-server distribution system allows Spyse to scan all over the world, bypassing location scanning restrictions and blocking from internet service providers. This makes for expanded datasets which are hard to obtain elsewhere.

Benefits Of Database Access
Spyse’s database stores over seven billion documents of hot data which can be accessed instantly. Employing fifty highly functioning servers with data broken up into 250 shards, users gain the benefit of having the largest flexible database on the web at their disposal.
This cyberspace search engine focuses not only on providing the raw data but on showing the connection between different parts of the internet.
Users will reveal interesting insights into corporation ties based on gathered technical data: like which companies exist on the same AS, connected through the assets, or which service is about to drop a new feature based or implement an update.
Data Providing
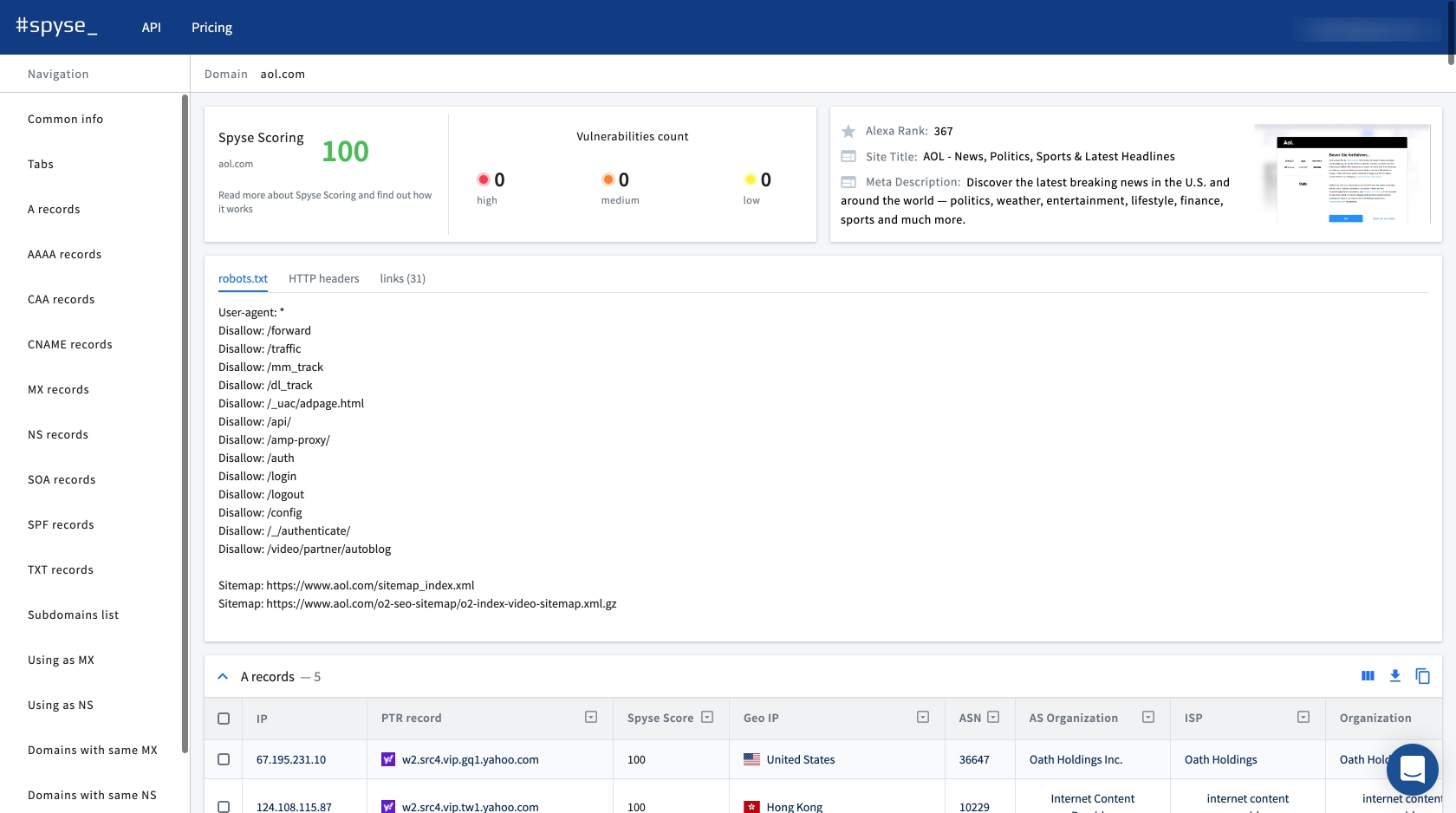
Users can access data on Spyse using their web interface and their API.
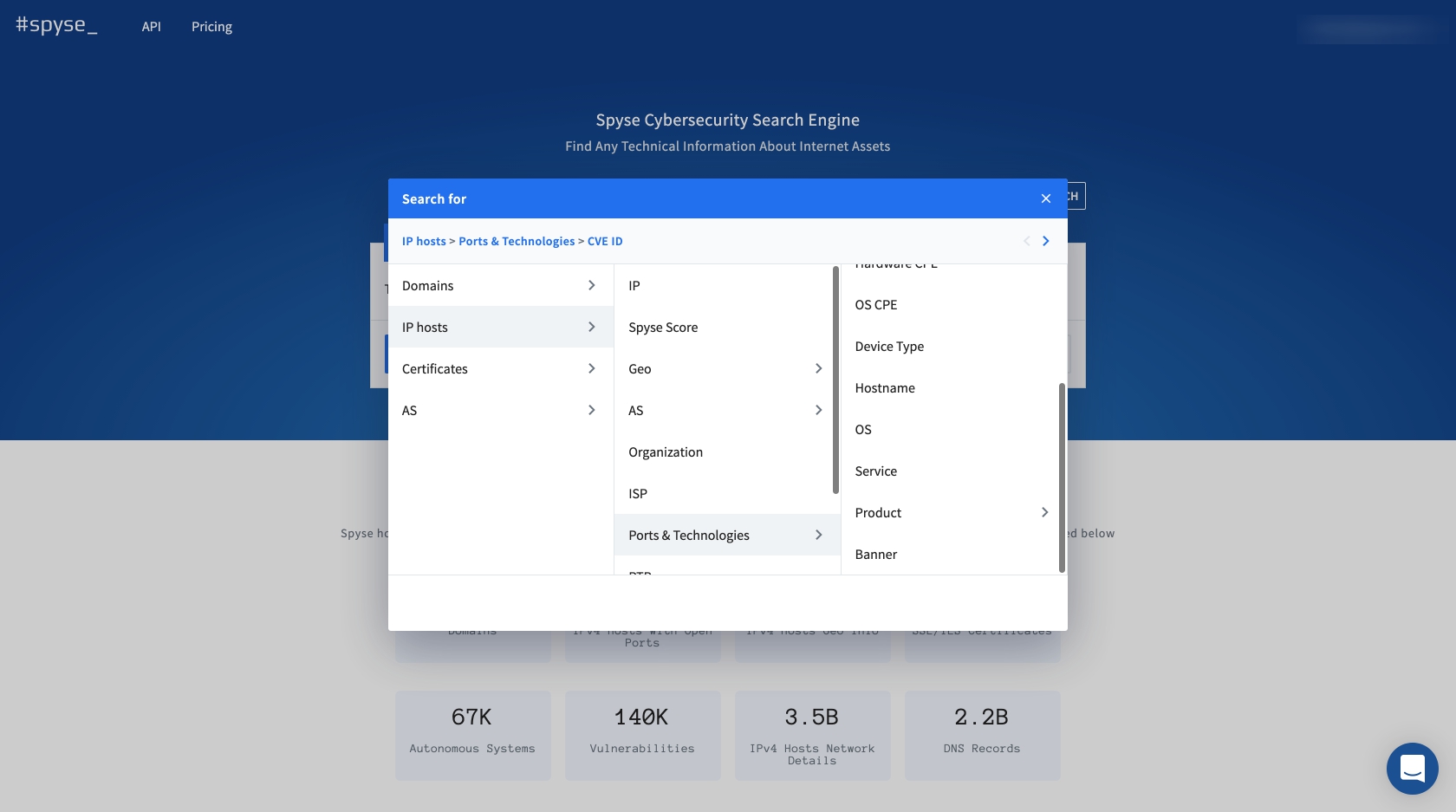
The web interface comes with many visual productivity perks. It’s a simple looking search engine which presents data in tables. These tables can then be adjusted to filter out unnecessary data, which makes it a perfect tool for finding precise results. All of the information found on the web interface can be downloaded for offline access.
Users can also integrate the Spyse search engine with their tools and services using their flexible API. The API allows users to obtain any information from Spyse’s database using lots of methods and types of requests. Also, all documentation is on Swagger which is a huge benefit.
The Search Engine does not have a CLI yet, but the team is reportedly developing one. They do have a Python wrapper for those in trend. It was made with outsourced developer zer0pwn, whose work many pentesters will recognize.
Additional Productivity Perks
Spyse engine offers two great tools for further boosting productivity and output.
Advanced search is the most interesting feature that allows users to implement up to 5 search parameters in one search query in order to maximize the output accuracy. This helps narrow down data, weed out unnecessary info, and get precisely what pentesters are looking for. For example: Perform SSL lookup to find expired certificates of some organization and filter all companies’ assets using security score. Filter them and you’ll get the list of the assets with expired certificates from the least to the most vulnerable elements related to this company.
Another cool feature is the Security Scoring. The Scoring basically compares the data crawled by Spyse scanners to a few CVE databases and assigns domains and IPs a security rating of 0-100, allowing to search, filter, and explore vulnerable elements using advanced search. It helps bug bounty hunters to quickly make a vulnerable target list, and sysadmins to keep track of their infrastructure security.
Specialists Who Benefit Most
Security specialists can use Spyse to analyze their cyber infrastructures much quicker and seal off vulnerabilities before they’re exposed by hackers. Having a tool like this will help companies stay safe online and give specialists a competitive edge over hackers.
Pentesters and bug bounty hunters will also find great benefits from Spyse. There is no need to create its own scan infrastructure, which takes up time and money. Pentesters can perform mock attacks and remain undetected and use this search engine when other methods are prohibited by bug bounty contract.
Overall, the Spyse cyberspace search engine is made especially for quick data gathering, maintaining a strong cyber-infrastructure, and performing competitive analysis.












 © 2024
© 2024
0 comments