Thousands More Men Have Been Duped By An International Tinder Hack

A British hacker operating under the name Catfi.sh claims to be running a similar operation, but on a far greater scale: instead of running one bot, Catfi.sh is running up to 20 dummy profiles in the US and the UK at any given moment. Since launching his program shortly after Valentine’s Day, he estimates he’s ensnared 10,000 male users and relayed 100,000 messages. Every day, Catfi.sh says 200 new users fall for his bots and 2,500 new messages are sent.
While Patrick designed his program as a joke with a slightly political bent, Catfi.shoriginally developed his to make his Tinder experience more efficient. In effect, he says, “I could trick other guys into talking to girls on my behalf.” He created a digital ventriloquist act by transforming his own profile into a dummy. When a woman “liked” his profile, the program connected her to a random male Tinder user who would then communicate through Catfi.sh’s profile. If the conversation was going well and approaching a date,Catfi.sh would come to life — reclaiming his profile and giving his ventriloquist the boot.
The system worked poorly, he says, but he discovered he could create the same double-headed catfish machine Patrick set up. “I realized how hilarious the results were,” he says, “and haven’t looked back since.”
Unlike Patrick, Catfi.sh didn’t set up a telephone number scrambler. Sometimes, he says, the conversations include hundreds of messages and last weeks. On these occasions he sometimes steps in to sever the connection. But with so many messages in motion, he doesn’t track the program as closely as Patrick. He believes that at least some of the men matched through his program have met up in real life.
People have built Tinder bots before, but the scope of Catfi.sh’s hack is staggering: he claims to currently have multiple bots operating in London, Glasgow, Manchester, New York, Houston, San Francisco, and elsewhere.
Echoing Patrick, Catfi.sh says building bots on top of Tinder’s API was “very trivial.”

“I was surprised by how little defense the Tinder API has,” he adds. His program ran 24/7, sending Tinder’s API tens of requests per second from the same IP for over a month with no interference. (Tinder eventually did ban his IP and he now runs the program through Tor.)
“I can only assume that they haven’t realized what’s going on, although this becomes difficult to understand since someone at their end has clearly looked into me — they’ve manually banned several of my Facebook accounts and also an IP address,” he says.
Reached for comment, Rosette Pambakian, Tinder’s VP of Corporate Communications and Branding says, “Keeping Tinder’s ecosystem safe and enjoyable for our users is our top priority. We apologize to those who were affected by this misuse of our platform. Although this is not a security threat, we take these violations very seriously and will take action against accounts that deceive our users.” She added that Tinder is looking to enhance anti-spam systems and add measures that would ensure that only Tinder clients can access the API.
In the meantime, Catfi.sh plans to continue running his bots. He’s read so many of the conversations that they’ve lost their novelty. “But my friends enjoy them,” he says, “so I don’t see a point to stop.”
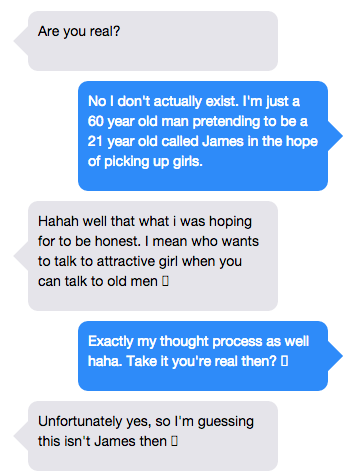
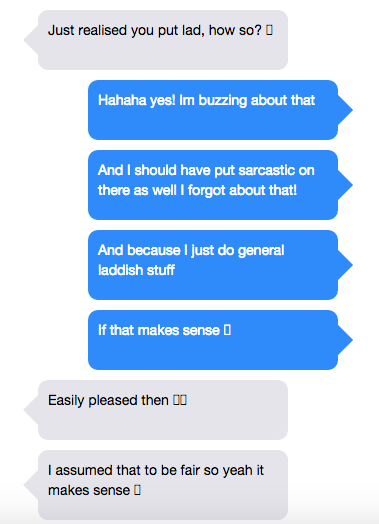
Catfi.sh went live with a site where he published 50 conversations he’s gathered. They represent just 1 percent of what he has in stock so far.
Does Catfi.sh think there are other hackers running similar programs out there? “Before Patrick, I would’ve said no….But there are lots of programmers out there with a slightly mischievous side. I wouldn’t be surprised if there was a third.”
Hacks like these pose an existential crisis for Tinder: social networks are built on trust, and if an individual can’t be certain whether they’re speaking with a crush, a bot, a marketer, or even a brick, the app loses value. But this hack also poses a second, more intriguing question: between Patrick, Catfi.sh, hackers like them, and the thousands they’ve fooled, how many men on Tinder are actually talking to a real woman?
Via TheVerge













 © 2024
© 2024
0 comments